Leave a Comment:
9 comments
Get the same error
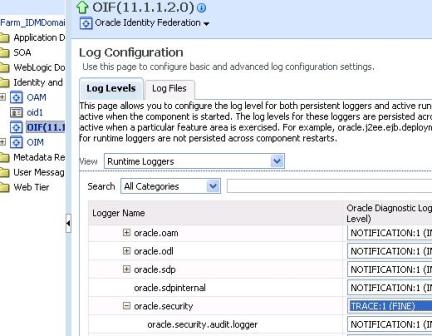
But even after increasing the trace it doesnt give me detailed error in the wls_oif1.log.
Please help
ReplyHi Atul,
I too have SP and IDP OIFs on two different machines. I have configured the two OIFs with each others’ metadata. In SP, I have put in the SP integration module to be OAM and have configured the same. However problem is once the OIF redirects me to IDP for authentication and I put in the credentials, I am not getting redirected to SP URL which I wanted to access. If I configure SP Integration module as Test SP Engine I am able to get the Authentication Successful SAML Details. But since I want redirection I set the above module and voila I have this error staring in my face.
The diagnostic logs tell me that there’s this error -“oracle.security.fed.event.EventException: com.oblix.access.ObAccessException: Unprotected resource GET http://vpunvfpctnsz-05.ad.infosys.com:8080/fed/user/oam/OIF-password-protected used in an ObAuthenticationScheme or ObUserSession constructor.” I checked in OAM and saw that this URL is automatically protected under the policy that is created by OIF by default i.e. the “OIF SP Policy – Do Not Modify”. Could you plz shed some light on this if you have any expreienced this before.
Thanks
Reply@ Sourabh,
Create a simple test HTML page called protected.html under OHS document root and in OAM protect this page by OIF authentication scheme and test URL http://ohs_host:ohs_port/protected.html
Hi Atul,
I have deployed the page at C:\Oracle\Middleware\user_projects\domains\OIFDomain\autodeploy\test through Eclipse. It was accessible directly as http://host:port/Test/SP_LandingPage.html.
During the configuration I was doing, I protected the /Test/SP_LandingPage.html using the OIF policy domain I had created in which I had also protected the /fed/user/authnoam needed for the OIF configuration. Both were protected with different policies. For instance I protected /fed/user/authnoam using OIF_Policy policy and the /Test/SP_LandingPage.html using SP_Landing Policy in that policy domain. After that if i try to access the SP_LandingPage i designed, it gets redirected to the /fed/user/spoam of which I am not sure what it might be. Then i get the /fed/idp/samlv20 so i think maybe this lead to sp initiated sso coz what i generally get on going through the idp website is the /fed/sp/authnresponse20 assertion before i get the error. Anyways so in this case i got this saml and then in next step it went to the idp website instead of opening the page. And this all happened without me providing any authentication for any user. Anyways this scenario aside, i want the user to go through idp itself and in that case i get the flow and error that i input in the first post. Any pointers?
Reply@ Sourabh,
Please update your requirement and I’ll suggest what to do .
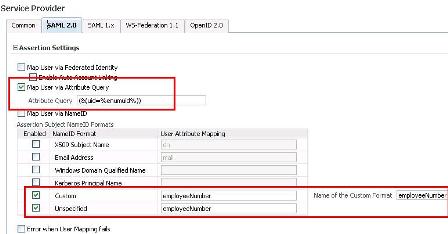
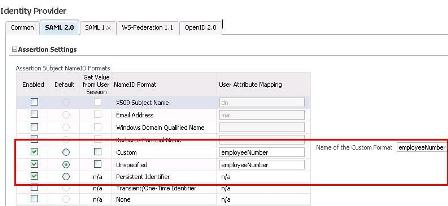
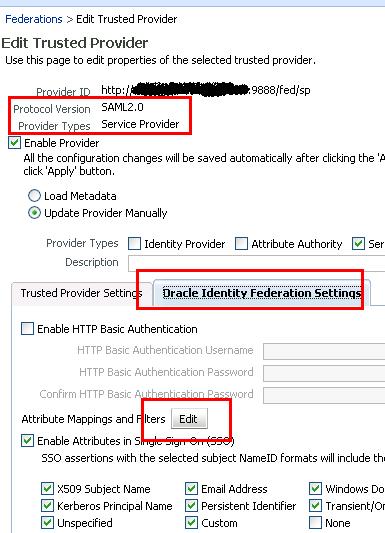
I am trying to simulate the scenario where federation exists between two partners. Service provider uses OIF to understand the SAML response from the IDP and hence authenticate user. It is a SP-Initiated SSO login. So when user tries to access a protected page i.e. the landing page here, he gets redirected to my custom login page and the URL of the place where he is now is set in a cookie simultaneously. He then puts in credentials. IDP checks these against its database and generates a SAML response. He is then redirected to OIF of SP with the SAML generated and is authenticated there using this and a session will be maintained for him. Now the problem in my simulation is that OIF is authenticating the user successfully as can be seen when I configure it to be Test SP Engine. However when I integrate it with OAM as SP Integration module, the user does not get redirected to the landing page he requested as set in the cookie nor is he getting logged in on IDP or SP. But configured as Test SP Engine, I am able to get the authnresponse20 page which has details of user login along with the fact that he was authenticated successfully. So how to achieve the redirection using the OAM configured as SP Integration module?
ReplyHi Atul,
I have very similar problem as described above.
But even after trying all I am not able to get pass this 401 Unauthorized error.
Its SP initiated SSO solution where OIF is integrated with OAM on SP side. Here the IdP is a third party custom built solution.
I am sending the SAML Request as well as SAML Response for reference. Please suggest what can be the issue.
baf2d952e92fc37704de69f06afc42058706c2658e2d09cb4a12160d655fb3d6
yOSkZ2wRb0SU7ixMvKjJ0DB0Xrw=
fO2+XK5ROIPA+HvsDtAyOWs6ZuX2WCq1WIi1jpHPUAyZ/dN5Zsda6ZoTrJ5pC7oeWY8vmaFk6Imx1loDze4e/5QqQ8xdwxUuUcz/6hDwq2WsUkFQy+uwU50dRbMa5Ae6vmjva6t6QWH20lLF3CE07ztnBg9uMF1AxXvLzVD5ns8=
\n AppleSSOnpaaNboab4PjwxkJbPAQgnue6BA=gYuI7kq/CJA8a+IHuX8xxrbXyacvqQ824MuWj7QgQAD2B9VRvQ5Tq+IsXgLj7PT9W+rpEa5AytbK\nKOynJN2H5msXJET6Q+M9XKpm8S036WAyqExXwBY5SJ1mxXNTX/Psvqv9fnHU7mWJOWAO7bPxrMRJ\nLe/ce8sSteEHIgxgzT/cMYtt0O/ptfN2Q+Xc8/JY38zcnBaImuIRKQUoiC9jVc69rn02N/Jtob44\nrPJhAmV1GTPmY53kWSD4z3OMfpFKs8v52I5gZhXb6KqTfZx2JQIy57afMqXAl5oXRaiGz5rCzIvc\nZybHwojoS65Cdikl2Kf3IH4Uout/lO4Ia3Sbqg==MIIEAjCCAuqgAwIBAgIIfuOqYCkbPUMwDQYJKoZIhvcNAQELBQAwfTEzMDEGA1UEAwwqVGVzdCBT\nU08gQXV0aCBSb290IENlcnRpZmljYXRpb24gQXV0aG9yaXR5MSQwIgYDVQQLDBtJU1QgQ2VydGlm\naWNhdGlvbiBBdXRob3JpdHkxEzARBgNVBAoMCkFwcGxlIEluYy4xCzAJBgNVBAYTAlVTMB4XDTEz\nMDUxNzIxNTQyNVoXDTE1MDUxNzIxNTQyNVowVDEiMCAGA1UEAwwZc3Nvc2FtbHNpZ24tdWF0LmFw\ncGxlLmNvbTEMMAoGA1UECwwDSVNUMRMwEQYDVQQKDApBcHBsZSBJbmMuMQswCQYDVQQGEwJVUzCC\nASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAORJuKEFq14tH9EhVt17zpDVRTIPE1J3qqZN\nP0QXnzSeoUVVTdoY+Na7r+k3kNbh91FCGM+MmBK3Sp4gDNv600cffdHhmXiDDprK9CqZJOcHnRn4\nNaXMH/U69aw8Fgmn7emQ7G0SAeobA5ljZYBWJJyj+Yi8T9vyNueEyFQOoviN1CjPJRjyp+N+vxFu\nkGoKCzYCw3M33MmBzIrSxmC164ri11T5JPJHqqcoICpy8iLZi3CPjjG9VMlUNbjrt0IY2e/6zUrm\nOoqnZnTKuGUwqcho6j6+KbT01tvQcwl7EKrVnlUqRAUdIkjFuTJkZb/1dsDCmMDaqQ0OK+nIeHJB\nmxMCAwEAAaOBrjCBqzBLBggrBgEFBQcBAQQ/MD0wOwYIKwYBBQUHMAGGL2h0dHA6Ly9vY3NwLXVh\ndC5jb3JwLmFwcGxlLmNvbS9vY3NwMDMtc3NvYXV0aDAxMB0GA1UdDgQWBBSwq+iNvZi1W9e341SH\nFatd1wdplDAMBgNVHRMBAf8EAjAAMB8GA1UdIwQYMBaAFASMk+jPVZacU1HYHgpziddijdY5MA4G\nA1UdDwEB/wQEAwIHgDANBgkqhkiG9w0BAQsFAAOCAQEAYlHVKCa27QGmLoFTME38EJdyllY5TkQB\nWIEcK0e5p6HHwD7RJL+bb8HFRUAzvsv57CfaaJ0ot/6wfG03+Co+2OBMCqTCybgjBsbbaB/2Vszt\nZVZx5JjovB8LE8d5342Gzr/shM+RVBrCAcNFd+1WiWNpJttwoh0/HBY9w4C+AwV8llQuUCaj73yA\nBU8zVDFWT7DejDHfJBNPWWHLmI3hpdhQWfjyWt5dzmxWwPG1Xz9Fxie1w3s5Ips55HcGvRwO5HgQ\n4PEILl29KcfYFk8jBX1hV/cVngc3eaA8+u8avnrqatCrFtPkXAxkMLLIXcDBYb3kZ5GMpxidPRSy\nN4FZuw==\n \n \n \n \n AppleSSO\n \n ritesh_kumar@apple.com\n \n \n \n \n \n \n \n baf2d952e92fc37704de69f06afc42058706c2658e2d09cb4a12160d655fb3d6\n \n \n \n \n urn:oasis:names:tc:SAML:2.0:ac:classes:PasswordProtectedTransport\n \n \n \n \n ritesh_kumar@apple.com\n \n \n \n \n
ReplyHi Atul,
I met the same problem Sourabh faced. Till now, any idea?
Thanks a lot!
ReplyI’ve been surding online greater than three hours lately, but I
by no means discovered any interesting article
like yours. It is lovely worth sufficient for me. In my opinion, if all website owners and bloggers made excellent content as you probablyy did, the web shall be a lot more
useful than ever before.